Morto Worm Attacks RDP
Morto - A new and virulent worm, dubbed Morto, raised reached online users. It’s spreading quickly, through the Microsoft Windows RDP (Remote Desktop Protocol (RDP). Though the days of worms such as Blaster and Code Red were long gone?
This worm is developing a large amount of outbound RDP traffic – is capable of compromising both servers and workstations-infecting machines that are completely patched.
Morto is an old-fashioned internet worm, which targets Windows workstations and servers by exploiting poorly-chosen weak passwords to spread via Remote Desktop Protocol (RDP) connections (port 3389). It’s possible if you had a large number of infected computers within your local network, that the amount of traffic generated by the Morto worm might be so significant that it would effectively clog your system.
In this time, the Morto worm has also received a lot of press attention we need to keep the threat in proportion. However, Sophos Labs has received a very low number of exports of this worm being seen in the wild. Possible reasons for the low number of Morot reports may be that Sophos customers have chosen better passwords on their shares, or because Sophos products had detection relatively early on for this compared to some competitors.
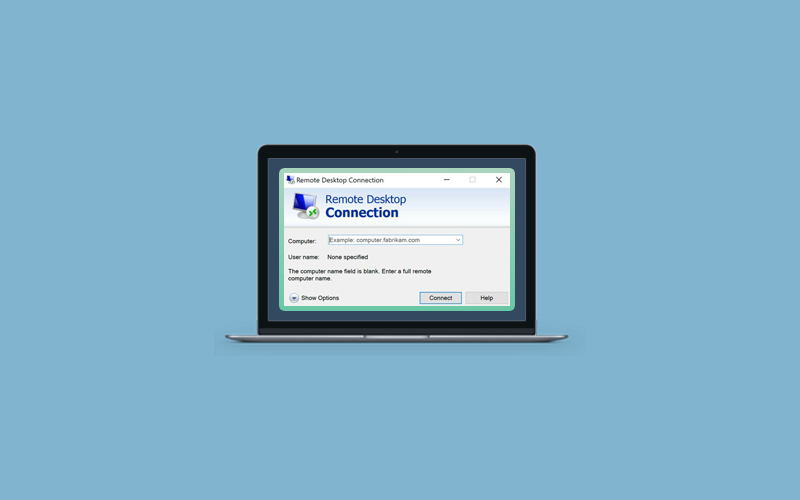
What is RDP?
RDP refers to Microsoft Desktop Protocol (RDP) provides remote display and input capabilities over network connections for Windows-based applications running on a server. Additionally, RDP allows users to control their remote Windows machines as if they were working on it locally (well, almost).
Morto Worm Spread via Remote Desktop Protocol
As we have read above, Morto is a computer worm and it spreads via Windows Remote Desktop Protocol (RDP) and infects Microsoft Windows workstations and servers. It was first appeared in August 2011, when network administrators started noticing heavy spikes in traffic on Port 3389/TCP.
Once Morto infects one computer on a network, the worm scans for other devices that have Remote Desktop Protocol enabled and copies itself to these computer’s local drives as a DLL file, which then created additional files on the computers. This worm can also be controlled remotely. There are currently two currently variants known by security experts.
How to Mitigate Morto Worm
Morto Worm is danger threat but still, it can be mitigated by following some basic security best practices.
First of all, make sure that you’re enforcing strong password choices on your user accounts. Not that the unique “Administrator” accounts password AWS automatically assigns to your instance upon launch complies with this recommendation and should be sufficiently strong to make brute force password guessing infeasible. In case, you’re using the EC2 Windows Configuration Service to override this automatically assigned password, please ensure that your selection is cryptographically strong.
In addition, you can also run an antivirus scan that prevents Morto and other types of malware as well. We recommend you to choose Waredot Ultimate that comes with the package of other advanced security protection. You can take the 30-day free trial and if you find it useful, you can purchase it.
Summary
Hey guys! This was the guide about “Morto worm attacks RDP.” This guide is a short description of Morto Worm and its troubleshooting. Hope you find this article helpful and informative. If you’ve any queries regarding this article, please let us know in the comment section. We would be glad to answer you!